1 3/4" I.D. Bearing Cone - 25580 - 3 4 bearing wheel
It represents the ease and speed with which attackers can exploit the vulnerabilities. We can mark Automatable as Yes if we can reliably automate steps 1-4 of the Kill Chain. Developed by Lockheed Martin, the Cyber Kill Chain® framework is part of the Intelligence Driven Defense® model for the identification and prevention of cyber intrusion activity. The model identifies what the adversaries must complete in order to achieve their objective.
If a vulnerability discloses authentication or authorization credentials to the system, this type of information disclosure should also be scored as Total if those credentials give an adversary total control of the component. This implies that Technical impact has a scope and is relative to the affected component where the vulnerability resides.
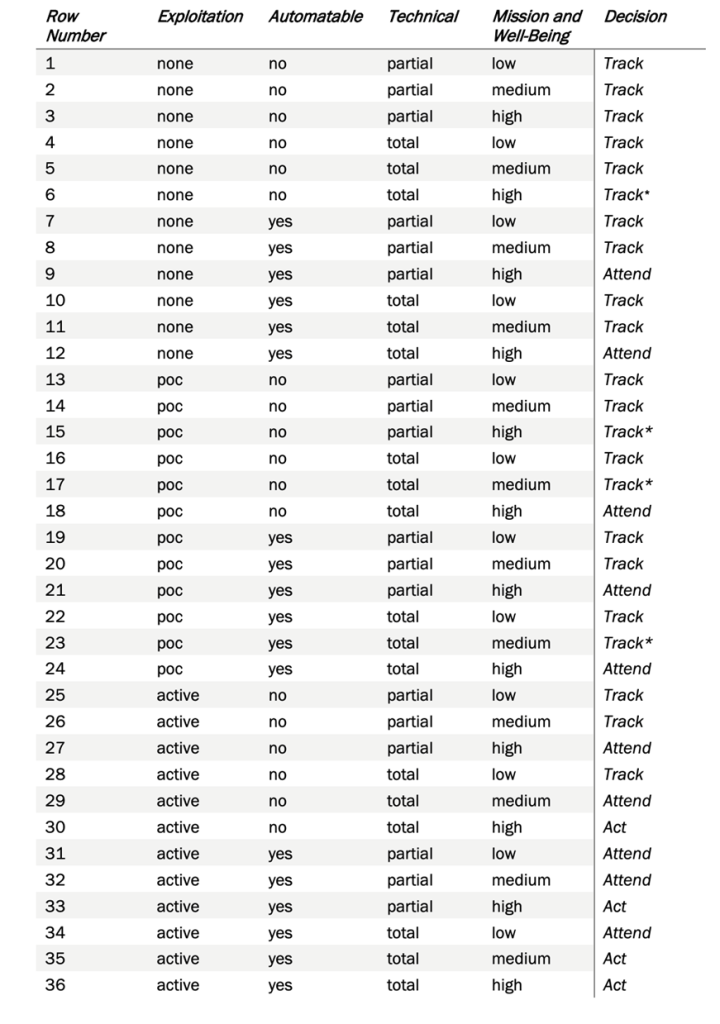
Stitching all the decision factors together gives a Decision Tree of CISA SSVC. It meticulously determines a vulnerability to be considered either as Act, Attend, Track*, or Track on a specific device. The same vulnerability on another device may fall into a different category (Act, Attend, Track* or Track) based on the characteristics analyzed while deriving the four decision points – Exploitation, Technical Impact, Automatable, and Mission Prevalence. Defying the fact that prioritization based on the severity score of a vulnerability would have resulted in vulnerabilities of two devices being considered as same priority, CISA’s Stakeholder Vulnerabilities Categorization provides a unique approach to the risk prioritization algorithms.
Any evidence of active exploitation of a vulnerability through various sources such as CISA Known Exploited Vulnerabilities (KEVs), other certified information from various internet sources, National Vulnerability Database (NVD) plays an important role in decision-making.
Another way of making decisions for Automatable is to identify barriers posed by the device that make it difficult for attackers to exploit vulnerabilities. Vulnerability Chaining and open connectivity to the internet can enable attackers to exploit a vulnerability by using other weaknesses. To decide on a value of No or Yes, analyzer algorithms must consider all reasonable scenarios.
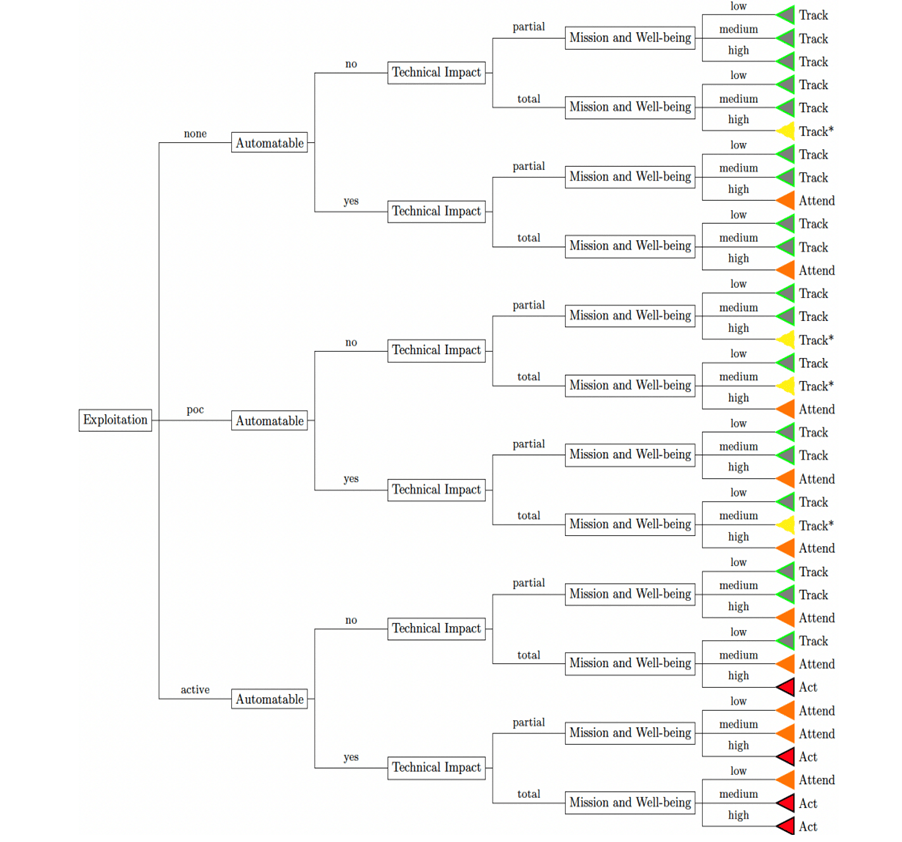
There are four factors that determine a vulnerability on a device to be one Act, Attend, Track*, Track. The decision-making points embrace reasonable assumptions made with a prior understanding of a vulnerability and scenarios. The four factors comprise Exploitation, Automatable, Technical Impact, and Mission Prevalence.
We, at SecPod, discovered a thought-provoking document from CISA on Stakeholder Specific Vulnerability Categorization (SSVC), a customized decision tree model that assists in prioritizing vulnerability response for customers by evaluating vulnerabilities. The goal of SSVC is to assist in prioritizing remediation based on the impact a vulnerability exploitation would have on the organization(s). The decision tree determines four possible outcomes for a risk – Track, Track*, Attend, and Act. The table below explains Vulnerability Decisions and Possible Outcomes.
This determines what is the impact on the Mission Essential Functions of Relevant Entities. A mission essential function (MEF) is a function directly related to accomplishing the organization’s mission as set forth in its statutory or executive charter. Identifying MEFs is part of business continuity planning or crisis planning. In contrast to non-essential functions, an organization “must perform a [MEF] during a disruption to normal operations.” The mission is the reason an organization exists, and MEFs are how that mission is realized.
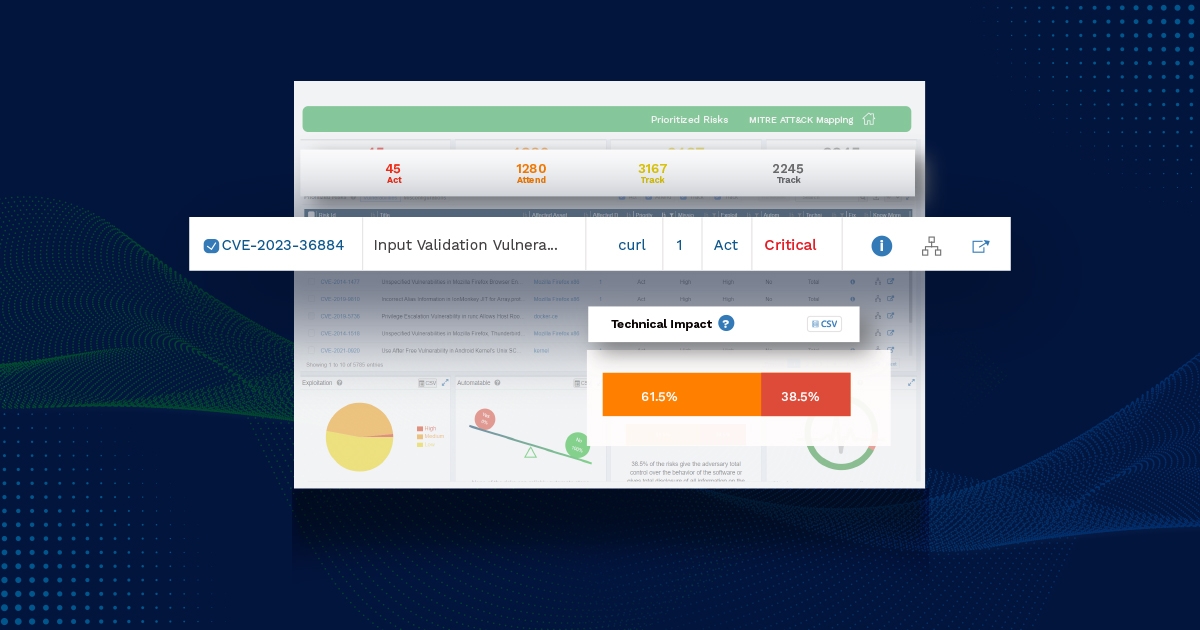
Risk Prioritization is not a new technology in the cyber security space. Cybersecurity professionals look for products that can integrate with existing vulnerability assessment reports to help prioritize risks, most often just software vulnerabilities. Primitive modus operandi such as Prioritization based on the Common Vulnerability Scoring System (CVSS) is an easy go-to approach for ordering mitigation plans. Should we also consider a step forward? What also matters is the stakeholders on which a vulnerability exists. Is the vulnerability on a mission-critical device Is there a mitigation or workaround already in place to avoid vulnerability attacks We not only base our decisions merely on software vulnerabilities but also look deep into the misconfiguration in the systems.



 8613869596835
8613869596835